iWorld
WhatsApp Pay goes live in India
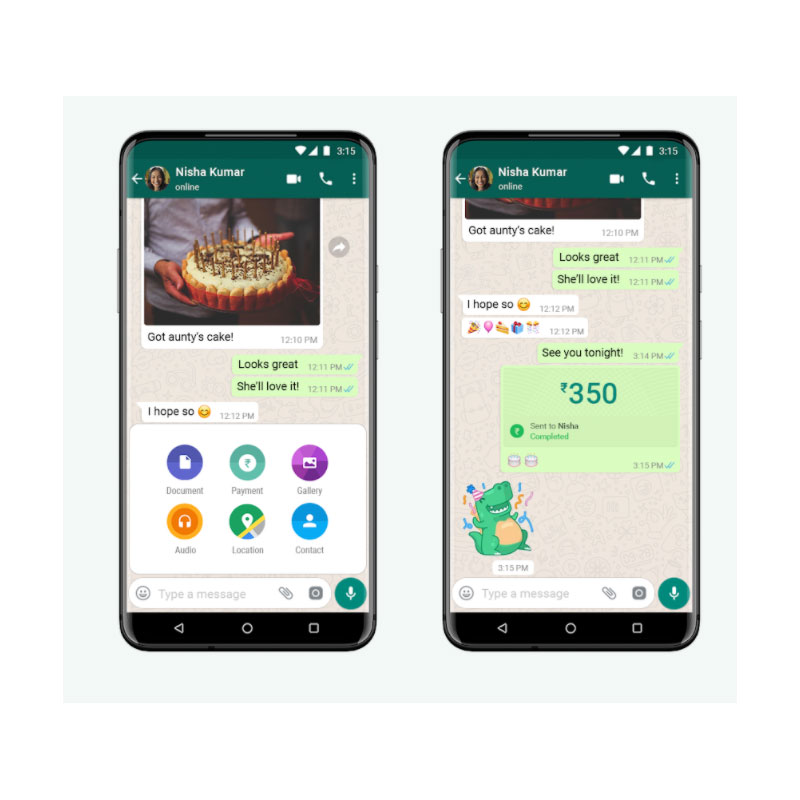
KOLKATA: In what could be a turnaround for India’s payments market, WhatsApp Pay has gone live today. WhatsApp’s parent company Facebook has been developing the payment feature for a while now, but regulatory hurdles were not easy to overcome.
The WhatsApp payment feature has been designed in partnership with the National Payments Corporation of India (NPCI) using the Unified Payment Interface (UPI). To carry out transactions via the messaging app in India, it’s necessary to have a bank account and debit card. WhatsApp sends instructions to banks that initiate the transfer of money via UPI between sender and receiver bank accounts. People can send money on WhatsApp to anyone using a UPI supported app.
The Indian digital payments market is already saturated with homegrown platform Paytm, big players like Google Pay, PhonePe, Amazon Pay, as well as a dozen other start-ups. But an enormous growing user base of 400 million, and a market value projected to reach $1 trillion in the next three years inspires confidence of having more than a fighting chance among new entrants like WhatsApp. Plus, the messaging app already enjoys immense popularity in the country, which also happens to be its largest market.
Starting today, people across India will be able to send money through WhatsApp This secure payments experience makes transferring money just as easy as sending a message. pic.twitter.com/bM1hMEB7sb
— WhatsApp Inc. (@WhatsApp) November 6, 2020
“In the long run, we believe the combination of WhatsApp and UPI’s unique architecture can help local organizations address some of the key challenges of our time, including increasing rural participation in the digital economy and delivering financial services to those who have never had access before,” the company stated in a blog post.
Just like every feature in WhatsApp, payments is designed with a strong set of security and privacy principles, including entering a personal UPI PIN for each payment, the app’s developers added. Payments on WhatsApp is now available for people on the latest version of the iPhone and Android app.

iWorld
Meta warns 200 users after fake Whatsapp spyware attack
Italy-targeted campaign used unofficial app to deploy surveillance spyware.

MUMBAI: It looked like a message, but it behaved like a mole. Meta has warned around 200 users most of them in Italy after uncovering a targeted spyware campaign that weaponised a fake version of WhatsApp to infiltrate devices. The attack, first reported by Agenzia Nazionale Stampa Associata, relied on classic social engineering with a modern twist: persuading users to download an unofficial WhatsApp clone embedded with surveillance software. The malicious application, believed to be developed by Italian firm SIO through its subsidiary ASIGINT, was designed to mimic the real app closely enough to bypass suspicion.
Meta’s security teams identified roughly 200 individuals who may have installed the compromised version, triggering immediate countermeasures. Affected users were logged out of their accounts and issued alerts warning of potential privacy breaches, with the company describing the incident as a “targeted social engineering attempt” aimed at gaining device-level access.
The malicious app was not distributed via official app stores but circulated through third-party channels, where it was presented as a legitimate WhatsApp alternative. Once installed, it reportedly allowed external operators to access sensitive data stored on the device turning a simple download into a potential surveillance gateway.
According to Techcrunch, Meta is now preparing legal action against the spyware developers to curb further misuse. The company, however, has not disclosed details about the specific individuals targeted or the extent of data compromised.
A Whatsapp spokesperson reiterated that user safety remains the top priority, particularly for those misled into installing the fake iOS application. Meanwhile, reports from La Repubblica suggest the spyware may be linked to “Spyrtacus”, a strain previously associated with Android-based attacks that could intercept calls, activate microphones and even access cameras.
The episode underscores a growing reality in the digital age, the threat is no longer just what you download, but where you download it from. As unofficial apps become increasingly convincing, the line between communication tool and covert surveillance is getting harder to spot and far easier to exploit.